How I Set Up a Personal Cloud Workspace at Home Without the Headache
Introduction
Imagine having your own private cloud workspace right in your home—accessible from anywhere, yet secure and low-maintenance. I recently built one, and the process was far simpler than I anticipated. In this article, I'll walk through the journey, compare the remote access protocols I've used (SSH, RDP, VNC), and explain why a private cloud workspace solves the very problems those protocols create.
The Appeal of Remote Access Protocols
Over the years, I've relied on SSH for command-line tasks, RDP for Windows remote desktop, and VNC for cross-platform screen sharing. Each protocol excels in its niche:
- SSH (Secure Shell) is ideal for secure command-line access and file transfers.
- RDP (Remote Desktop Protocol) offers a rich graphical experience on Windows networks.
- VNC (Virtual Network Computing) provides platform-agnostic screen sharing.
These tools are indispensable for remote work, but they also introduce a significant drawback: they expose entire desktops or command-line environments to the internet.
The Hidden Costs of Remote Access
When you open a remote access protocol to the outside world, you're essentially granting access to a full PC. That machine requires constant maintenance:
- Regular security patches to prevent exploits.
- Firewall configurations to limit exposure.
- Vulnerability monitoring for each protocol's unique attack surface.
Moreover, if that machine is compromised, your entire network could be at risk. The convenience of remote desktop access often comes with a heavy security burden.
Why a Private Cloud Workspace Changes the Game
A private cloud workspace centralizes your applications and data into a secure, isolated environment. Instead of exposing a full desktop, you expose only the services you need—like a web-based file manager or a remote development server. This drastically reduces the attack surface. Plus, you can use modern tools like Docker or Kubernetes to deploy and manage services with minimal overhead.
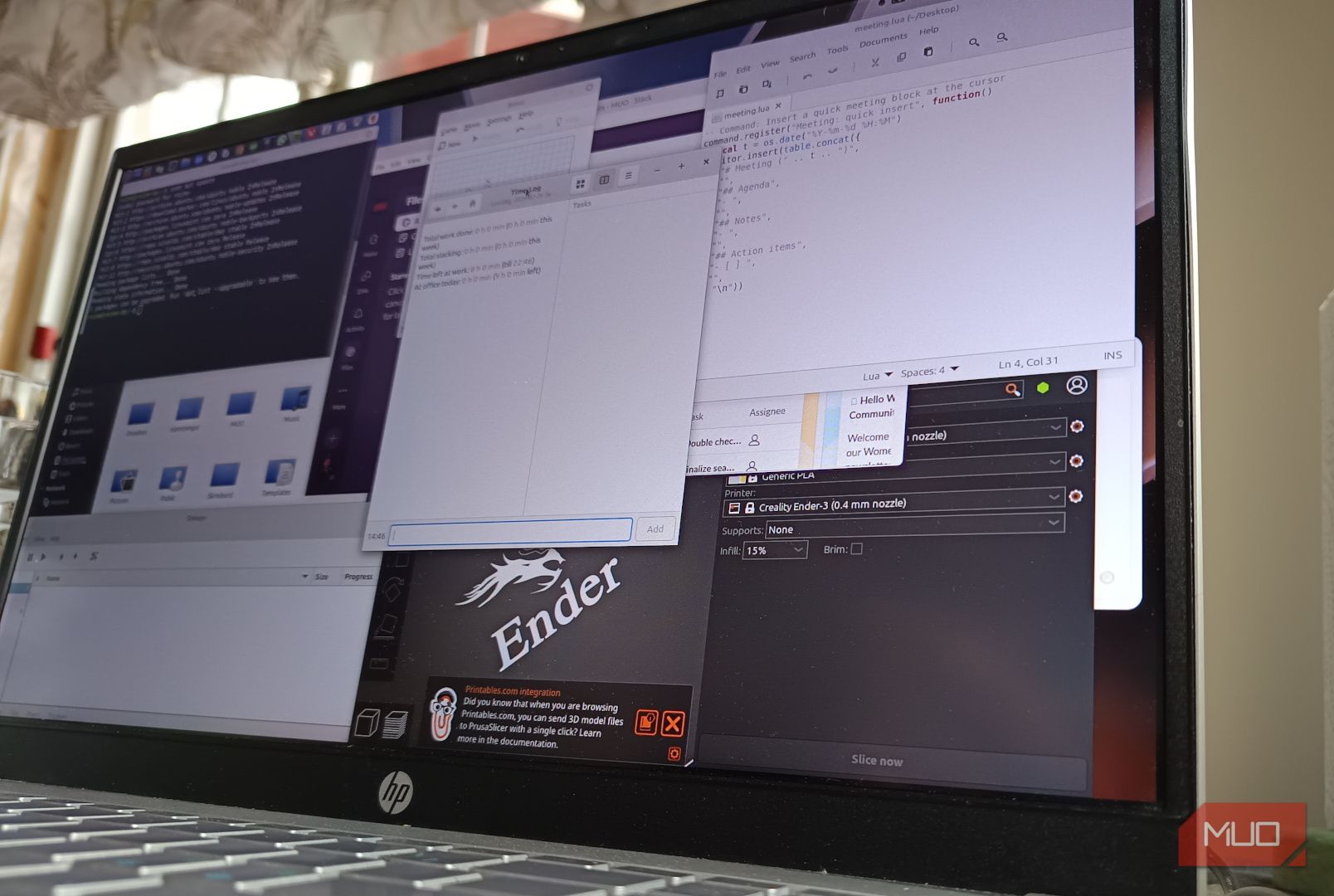
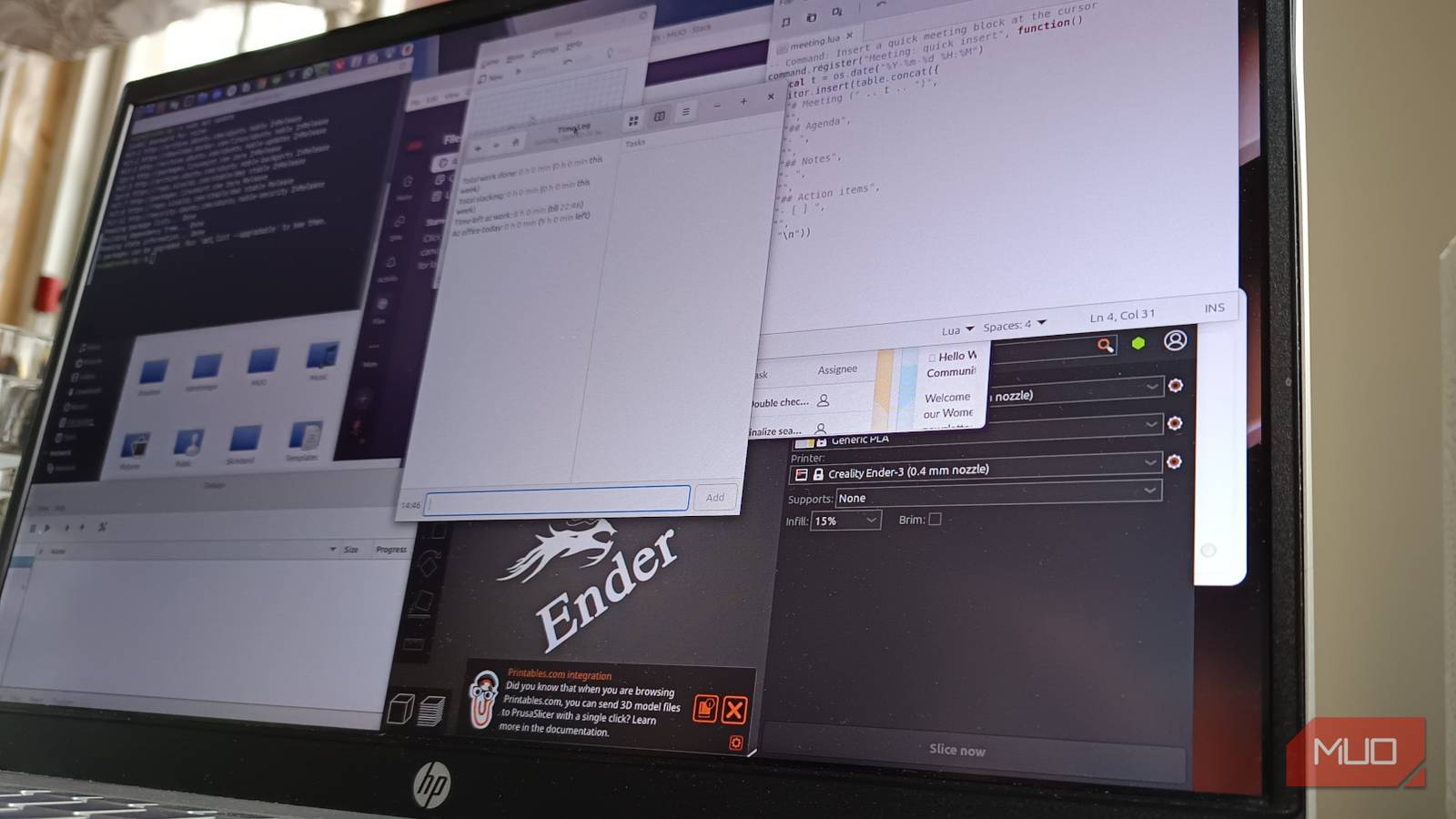
My Experience Building It
I started with a spare laptop running Linux and installed a lightweight container orchestration platform. Then I set up a reverse proxy (like Nginx) with SSL to handle incoming connections. The entire process took a weekend, and I was surprised at how little maintenance it required afterward. Now I can access my development environment, file storage, and even a few personal web apps from anywhere—without worrying about patching a full desktop OS.
Security First
I implemented key-based authentication, disabled password logins, and used fail2ban to block brute-force attempts. For additional layers, I recommend a VPN or Cloudflare Tunnel.
Performance Optimizations
Since I'm not streaming an entire desktop, bandwidth usage is minimal. Web apps respond quickly, and I can still use SSH for command-line work. If you need graphical applications, consider Web-based RDP solutions like Apache Guacamole.
Low Maintenance
With containers, updates are as simple as pulling new images. The host OS only needs occasional security patches, and the reverse proxy handles SSL certificate renewal automatically via Let's Encrypt.
Conclusion
Building a private cloud workspace at home was not only easier than expected but also eliminated the headaches of managing remote desktop infrastructure. By moving from full-desktop remote access to a service-oriented cloud setup, I gained security, simplicity, and peace of mind. If you've been hesitating to try it, I encourage you to start small—you might be surprised how straightforward it can be.
Ready to build your own? Start with a Raspberry Pi and a few Docker containers. The journey is rewarding.
Related Articles
- How to Become a NASA Astronaut and Prepare for a Spaceflight Mission: A Step-by-Step Guide Inspired by Dr. Anil Menon
- How to Assess the Atlantic Meridional Overturning Circulation (AMOC) Tipping Risk: A Step-by-Step Guide
- Revolutionary Discovery: Fat Metabolism Protein Found to Have Two-Faced Role in Obesity
- 8 Fascinating Facts About the Pleiades 'Seven Sisters' and Their Ghostly Blue Veil
- 10 Groundbreaking Facts About NASA's Supersonic Mars Helicopter Blades
- Hybrid AI Development Surges as Enterprises Bridge Low-Code and Full-Code Divide
- How to Trace the Origins of the Coruna Exploit Kit: Linking It to Operation Triangulation
- How to Evaluate Extreme Weather Forecasts: Why Traditional Models Still Outperform AI